Infosec stories - Page 26

Intruder uncovers 42,000 leaked tokens in web apps
Sat, 10th Jan 2026
#
devops
#
cloud security
#
application security
Intruder finds over 42,000 sensitive tokens hidden in JavaScript bundles, exposing a major blind spot in modern web app security tools.

HP warns of surge in polished fake updates & malware
Fri, 9th Jan 2026
#
malware
#
virtualisation
#
mfa
HP reports a surge in convincing fake software updates and staged prompts that trick users into installing stealthy, rapidly evolving malware.

Kiteworks & Concentric AI partner on data security
Fri, 9th Jan 2026
#
data protection
#
encryption
#
cloud security
Kiteworks and Concentric AI join forces to tie AI-driven data discovery to automated controls on sensitive information shared externally.

Thales unveils AI Security Fabric for runtime threats
Fri, 9th Jan 2026
#
data protection
#
hybrid cloud
#
digital transformation
Thales launches AI Security Fabric to shield enterprise LLM and agentic AI apps from runtime threats like prompt injection and data leakage.

OWASP unveils first Top 10 risks for agentic AI use
Fri, 9th Jan 2026
#
data protection
#
endpoint protection
#
digital transformation
OWASP has launched its first Top 10 list for agentic AI, warning autonomous systems act as a powerful but risky new digital workforce.

AI-native malware & deepfakes to dominate 2026 cyber risk
Fri, 9th Jan 2026
#
malware
#
data protection
#
ransomware
AI-native malware, deepfake fraud and attacks on connected devices will dominate enterprise cyber risk in 2026, VIPRE has warned.
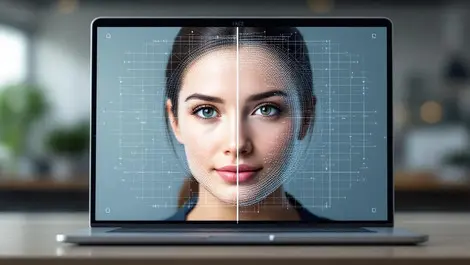
iProov, HYPR join forces to combat AI-driven deepfakes
Fri, 9th Jan 2026
#
surveillance
#
biometrics
#
mfa
iProov and HYPR integrate liveness checks with passwordless login to stop deepfake workers infiltrating enterprises at onboarding.

AI identities expose gap in modern privileged access
Fri, 9th Jan 2026
#
hybrid cloud
#
digital transformation
#
pam
Just 1% of organisations fully use Just-in-Time privileged access, leaving AI agents and cloud systems exposed to “always-on” credentials.

FIRST marks record growth in global cyber defence
Fri, 9th Jan 2026
#
firewalls
#
ransomware
#
advanced persistent threat protection
Global cyber defence group FIRST reports record 2025 growth, topping 820 member teams and expanding technical, training and capacity work.

Zynap raises EUR €6 million to scale AI cyber defence
Thu, 8th Jan 2026
#
advanced persistent threat protection
#
socs
#
ai
Barcelona cyber start-up Zynap raises EUR €6 million seed extension to scale its AI-driven preventive defence platform globally.

AI to Transform Procurement via Data and Security Leads
Thu, 8th Jan 2026
#
data protection
#
digital transformation
#
rpa
AI is set to transform procurement by 2026, making data governance, security and human-machine collaboration central to buying decisions.

Makop ransomware group sharpens tools in India focus
Thu, 8th Jan 2026
#
firewalls
#
ransomware
#
encryption
Makop ransomware pivots to India with RDP brute force, privilege exploits and GuLoader as it leans on basic flaws over bespoke tools.

The future of authentication in 2026: Insights from Yubico's experts
Thu, 8th Jan 2026
#
data protection
#
mfa
#
crypto
Yubico experts say 2026 will redefine authentication, with post-quantum security, digital ID wallets and AI-driven threats converging.
Keeper adds zero-knowledge secrets manager to JetBrains
Thu, 8th Jan 2026
#
data protection
#
devops
#
encryption
Keeper launches a zero-knowledge secrets manager extension for JetBrains IDEs, aiming to eliminate hardcoded credentials in codebases.
Proofpoint warns of surge in Microsoft device code phishing
Thu, 8th Jan 2026
#
edutech
#
mfa
#
cloud security
Proofpoint flags a sharp rise in Microsoft 365 account takeovers via device code phishing, hitting firms from finance to government.

Black Kite unveils tool to analyse third-party software risk
Thu, 8th Jan 2026
#
saas
#
supply chain
#
risk & compliance
Black Kite launches Product Analysis tool to expose hidden risks in third-party software, from SaaS subdomains to SBOM dependencies.
Nudge Security adds new tools to govern AI in SaaS
Thu, 8th Jan 2026
#
data protection
#
cloud security
#
socs
Nudge Security unveils expanded AI-in-SaaS controls to monitor chatbot use, browser activity and risky integrations across cloud apps.

AI cyber threats outpace stretched security teams by 2026
Thu, 8th Jan 2026
#
data protection
#
digital transformation
#
mfa
AI-powered cyber attacks are outpacing thinly staffed security teams, as firms prioritise defence but starve programmes of people and budget.

Checkmarx buys Tromzo to boost AI-driven code security
Wed, 7th Jan 2026
#
devops
#
application security
#
advanced persistent threat protection
Checkmarx snaps up AI start-up Tromzo to fold reasoning-based agents into its AppSec platform and speed autonomous code security.

Storm-0249 hijacks security tools to fuel ransomware
Wed, 7th Jan 2026
#
malware
#
firewalls
#
ransomware
Storm-0249 hijacks trusted security and Windows tools to stealthily broker high-value network access for ransomware operators.