Weak passwords expose systems and infrastructure risks
Thu, 7th May 2026
Cybersecurity specialists warn that weak password practices continue to expose consumers and critical infrastructure operators to growing digital and physical risks. The calls for action come as organisations and individuals mark World Password Day.
Industry executives say the focus on login credentials now extends far beyond simple access control. As digital services scale and converge, they increasingly tie password security to the resilience of data, systems and physical assets.
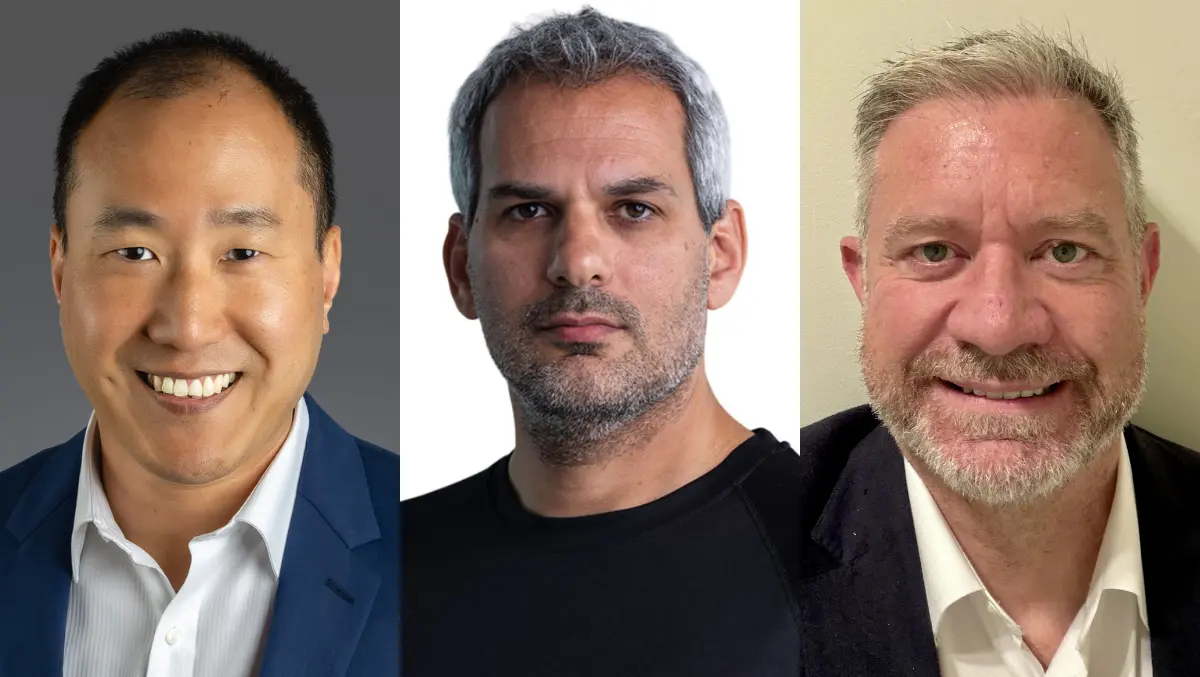
Jeff Park, Country Manager ANZ at Seagate, said organisations often overlook the storage layer when assessing password and access risks.
"World Password Day is a reminder that securing access to our digital lives is essential-but it's only one piece of the broader data security picture. Data is the lifeblood of today's digital economy, growing rapidly in both volume and value across personal and enterprise environments. As attention shifts beyond access to how data is stored, protected and preserved, secure storage becomes a foundational layer of trust, ensuring information remains safe, accessible and resilient over time. Ultimately, there is no data security without secure storage. As data continues to grow in importance, so must our commitment to protecting it, so it remains available, recoverable and secure when it matters most," said Jeff Park, Country Manager ANZ, Seagate.
Critical systems
Security leaders in the industrial and public sectors are also highlighting the risks that default passwords and manual processes create for operational technology.
Jason Pearce, Field CTO APJ at Claroty, said basic login combinations remain common on critical systems.
"World Password Day is a timely reminder that despite years of warnings, 'admin/admin' remains the skeleton key to the world's most critical infrastructure. Shockingly, many important systems are still protected by these weak, unchanged default logins. In the realm of Cyber-Physical Systems (CPS), weak or default passwords aren't just a digital vulnerability-they are a direct threat to physical safety and operational uptime. As organisations continue to bridge the gap between IT and OT systems without the proper security in place, they are essentially leaving the front door unlocked to our power plants, water systems and hospitals for any adversary with a basic search engine and a bit of persistence," said Jason Pearce, Field CTO APJ, Claroty.
He added that manual password processes are no longer fit for purpose in complex industrial networks.
"To shut this door, organisations must move past manual password management and embrace automated exposure management instead. Humans cannot feasibly manage hundreds or thousands of passwords at once-in many cases, they can't even identify every device on their network. Any effective exposure management program must start with total visibility into every connected asset across the XIoT. That should be followed by secure access controls that wrap legacy systems in modern security layers such as multi-factor authentication (MFA). On this World Password Day, the goal shouldn't simply be 'have better passwords'. Instead, organisations should aim for a zero-trust architecture that ensures a single compromised credential can't take down an entire production line, power grid or health care facility," added Pearce.
Human factor
Others in the security research community argue that the underlying problem lies in human behaviour rather than in passwords themselves.
Tomer Bar, Associate VP of Security Research at Semperis, said common ideas about password strength often fail in real-world conditions.
"Passwords have a terrible reputation, but that's not really the password's fault. It's ours. Most of the risk comes from human limitations and predictable behaviour. The comforting myth is, 'if the number of possible combinations for a 10-character password using lowercase letters, uppercase letters, digits and special characters is enormous, then the password must be safe'. The total search space is in the order of tens of quintillions of combinations. Even if an attacker can test 1 billion guesses per second, it would take roughly 1,700 years to exhaust the entire space with a pure brute-force attack," said Tomer Bar, Associate VP of Security Research, Semperis.
But attackers exploit predictable password structures rather than the full mathematical range of combinations.
"On paper, that looks great. It's misleading, because very few people choose random 10-character passwords. Humans tend to fall back on predictable patterns: a capital letter first, followed by one or more lowercase letters, then one to four digits, often a year, and finally a single special character at the end. Advanced attackers know this. They don't brute-force the entire key space; they brute-force your habits, making passwords much quicker to guess. If you keep using passwords, the best practice is to stop letting humans design them. Use a password manager to generate and store long, truly random passwords of 20 or more characters, and never reuse them. Turn on MFA wherever possible so stolen passwords are far less useful. For the few passwords you must remember, use long, unique passphrases made of random words instead of lyrics, quotes or clever patterns. The goal is to make attacking you so difficult and unprofitable that attackers move on to easier targets," added Bar.